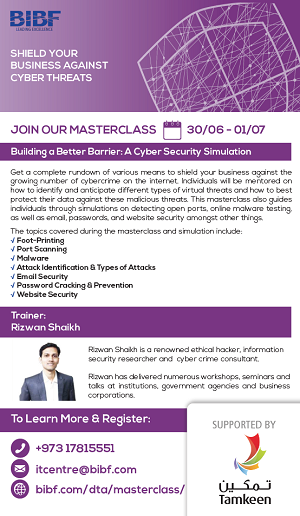
Course Description
This two day cyber security masterclass offers a complete rundown of various means for business professionals to shield themselves against the growing number of cybercrime on the internet. Individuals will be mentored on how to identify and anticipate different types of virtual threats and how to best protect their data against these said malicious threats. This masterclass also guides individuals through simulations on detecting open ports, online malware testing, as well as email, passwords, and website security amongst other things.
Learning Outcomes
By the end of this course, participants shall be able to:
- Understand how hackers gather sensitive data on their target before hacking and build protection strategies accordingly
- Learn how global IP addresses are allocated
- Understand how to secure an organization/business online
- Practice how to stay anonymous
- Identify spoof emails
- Understand how malwares are identified and created
- Understand how passwords are broken and how to take countermeasures
- Understand the basics of web security
- Implement Cyber Hygiene measures and controls for individual and business protection
Content Highlights
- Foot-Printing
- Types of Foot Printing
- Methods & Techniques
- Finding IP, OS of website
- Port Scanning
- Tools
- Types of Port
- Virtual port numbers
- Detecting Open ports
- Anti-Port scanning Methods
- Countermeasures
- Finding open port for any domain name
- Preparing entire Foot Printing report
- Malware
- Trojan
- Keyloggers
- Virus & Worms Concepts
- Bat File Scripting
- Countermeasures
- Blocking harmful batch files script
- Testing Malware online
- Identify Attacks
- Web Proxy
- Proxy Bouncing
- Performing Proxy Bouncing
- Introduction of TOR browser
- Dark web
- Email Security
- Various Protocol of Email
- Email Spoofing
- Sending spoof email
- Review Email Header
- Use mail Tracker
- Domain and IP Blacklisting
- Countermeasures
- Password Cracking and Prevention
- Complexity of password
- Password cracking Techniques
- Cracking web based Passwords
- Kali linux Tools introduction
- Installing kali Linux, creating password email account, cracking it
- Countermeasures
- Other types of Attack
- DoS & DDoS Attack concepts
- Social Engineering attack
- Steganography and Steganalysis
- Hiding data behind image using stenography technique
- Website Security
- Google Dorks
- Using google Dork to find sensitive information
- Defending against basic SQLi website hacking
- SQL Injections Basics
Date(s)
30 June - 1 July 2019
Time
9 AM - 3 PM
Register Now
To register for the course, please fill in the details below and a BIBF representative will attend to you within the next 24 hours.